Security advisor columnist Roger Grimes wrote an interesting piece on the evolution of corporate data security. He used Maslow's Hierarchy of Needs as his model. Briefly, here is Grimes’ Hierarchy of Security Needs:
-
In Stage One, no
one thinks about computer security at all. Passwords are short and
shared logons are common, no firewalls are installed, and the only
anti-virus software they have came preinstalled on some new machines
(and hasn’t been updated since). Nothing is encrypted or authenticated.
Infected and compromised machines are so common that most employees
keep using them even when they know they have problems.Eventually e-mail worm outbreaks attack networked medical devices, compromised systems are discovered, and some machines are constantly down
or slow because of malware attacks. One day a big security event happens, and patient identifiable data is lost or stolen. -
In Stage Two,
management and IT "get serious" about computer security.
Anti-virus software is purchased for e-mail servers or installed on
user desktops. A network firewall is installed (but with an
allow-by-default rule set), password lengths increase, and end-users
are educated about the most common threats.Success! Worm and spyware outbreaks happen
less often, but entire systems still go down a few times a year.
If a major worm or virus gets announced in the media, it always hits
the company badly. Another major security event happens, just as bad as
the first one. Things aren’t fine. -
A real security
officer (you know, with a security certification or training) is hired or
created. All employees sign an acceptable use policy when they are
hired, and passwords get longer and are required to be changed at least
twice a year. There's a focus on automating computer security.
Anti-virus software is installed on all desktops and automatically
updated from location-specific servers, patch management software is
utilized, and additional scanning programs to find malicious software
are set up.Viruses
and spyware are finally under control. External threats are minimized.
Then an employee is caught hacking the system and an IT manager is
caught reading management’s e-mails. Internal threats become a very
real problem. -
Management tells HR and IT to work on computer security policy, and to penalize employees who fail to follow proper guidelines.
Some sort of industry guideline or legal compliance legislation (HIPAA, SOX, GBL, and others) kicks in, adding to company security policy. Passwords are complex and changed once a quarter.
Dangerous e-mail attachments are blocked at the gateway. IT is interested in buying systems with hardened servers. The security team is actually brought in at the
beginning of projects, and software developers are trained in secure
coding.Still,
some security events happen. Some employees are still opening every
email attachment no matter how many times you educate them. Eventually,
a confidential database is breached from the outside, and tracked to a
compromised internal employee’s computer. All they did was install the
latest cool thing off the Internet. -
Self-actualization.
The security team and management finally understand that
allow-by-default and deny-by-exception policies will never work. Strict
computer policies are enacted, end-user desktops locked down, and
deny-by-default polices implemented everywhere. Corporate computer
images are the only ones allowed on the network. Employees caught
trying to circumvent security policy are fired.Patches
are thoroughly tested and deployed according to a criticality rating.
Vendor software must meet certain security requirements before it can
even be considered for purchase. All confidential data is encrypted by
default. Laptops and PDAs must have bootup passwords and data
encryption. Authentication is built into corporate logons, e-mail, and
physical security.
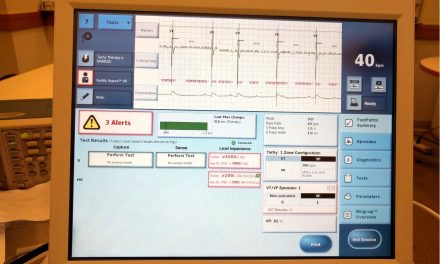
Adequate accommodation for networked medical devices must also be taken into consideration. And IT and Biomeds must forge a good working relationship that ensures both data security and patient safety.
Where does your organization fall in the hierarchy? A more interesting question, especially if you're a provider, is where do your vendors fall in the hierarchy?




Trackbacks/Pingbacks