Last November Kapersky Labs made some medical device security threat predictions for 2018 on their SecureList security bulletin. Kapersky has forgotten more about security than I know, but my understanding of health care and the medical device world allows me to offer some perspective and corrections to Kapersky's predictions. Let's review the relevant predictions:
Attacks targeting medical equipment with the aim of extortion, malicious disruption or worse, will rise. The volume of specialist medical equipment connected to computer networks is increasing. Many such networks are private, but one external Internet connection can be enough for attackers to breach and spread their malware through the ‘closed’ network. Targeting equipment can disrupt care and prove fatal – so the likelihood of the medical facility paying up is very high.
I will bow to Kapersky's grasp of the threat environment, and there is a growing number of network connected medical devices. However there are some quibbles with the details. Their perception of the risks are both greater and less than they suggest. A large majority of networks with connected medical devices are connected to the Internet; there are few truly private networks in hospitals or other care delivery organizations — this increases risk.
Hacked medical devices are a problem, and theoretically this can present a safety-critical risk. But I have yet to see a documented case of a patient injury or death reported that is attributed to a hacked medical device. The most realistic risk faced by providers lies with medical devices rendered unavailable due to malicious code — risk is lessened in this case.
There will also be a rise in the number of targeted attacks focused on stealing data. The amount of medical information and patient data held and processed by connected healthcare systems grows daily. Such data is immensely valuable on the black market and can also be used for blackmail and extortion. It’s not just other criminals who could be interested: the victim’s employer or insurance company might want to know as it could impact premiums or even job security.
This prognostication is true if, "connected healthcare systems," includes more than networked medical devices. Little if any of the data in medical devices is of value to criminals. It is true that data stolen from EMRs, patient accounting systems and similar information systems are much more valuable than run-of-the-mill personal or credit card data. Other than patient's name, none of this kind of information is available in medical devices. And while employers and payors might be interested in knowing certain medical things about the patient, I doubt any employer or payor in the US would pay criminals for this data. This prediction does not appear to apply to medical devices.
There will be more incidents related to ransomware attacks against healthcare facilities. These will involve data encryption as well as device blocking: connected medical equipment is often expensive and sometimes life-critical, which makes them a prime target for attack and extortion.
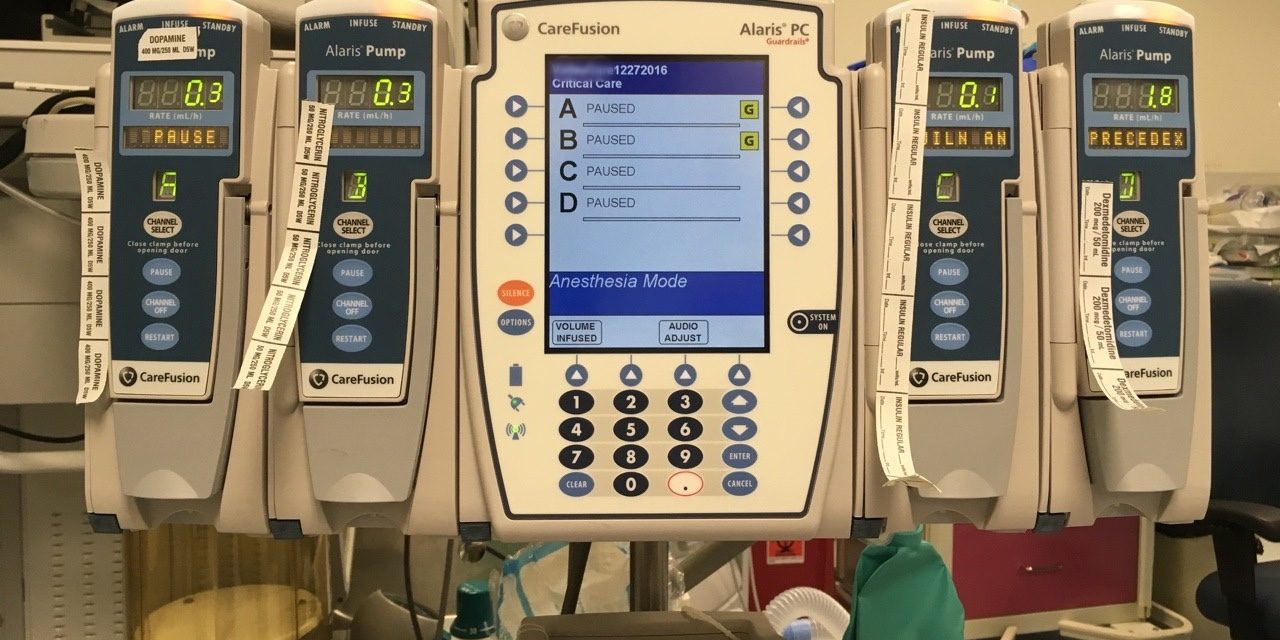
Jackpot! Should the CT or MRI at a hospital become ransomed by a hacker, I suspect that most provider organizations would pay the ransom ASAP. And given the costs of losing availability of those imaging modalities, they could easily justify paying 4 to 5 figures in ransom per modality. Ditto for a patient monitoring system or infusion pump system, which could present a substantial safety-critical risk.
Medical device systems using Microsoft Windows operating systems have suffered from malicious attacks for years from exploits targeting desk top computers. And I suspect there are many medical device systems currently in use that still run Windows NT, an operating system with many known vulnerabilities that is no longer supported by Microsoft. A ransomware attack is a different animal and it is not clear to me how a typical Windows ransomware attack targeting general purpose personal computers would play out on an ultrasound system, MRI or other embedded system device.
Unlike CT or MRI systems, most medical devices are really embedded systems with network connectivity and server applications added as an afterthought. Attackers could inject ransomware onto the servers to which embedded system devices are connected, but ransoming an embedded system device is another story. An embedded system device could perhaps be bricked — the equivalent of ransomware destroying data — but would be technically difficult to ransom. Most medical devices use firmware to store applications and data, and have very limited and specialized user interfaces. To be ransomed, a device must have a rewritable data storage device like a hard drive, and must have a user interface that can reliably display the ransom demand and allow those that pay the ransom to enter a key with the hope of restoring their device. (Yes, firmware can be rewritten, but extra technical effort is required to do this compared to a general purpose storage device like a hard drive.)
What's missing here is an exploit specifically geared for medical device systems. It would be a very bad thing should someone develop an exploit specifically for a widely used medical device system, say Philips patient monitoring, Carefusion infusion pumps or big diagnostic imaging modalities. Besides the potential for very widespread disruption in the use of those devices, there would also be some degree of safety-critical risk of patient injuries or deaths. Such an episode of attacks would rock the health care industry in numerous ways.
The good news is that developing such a targeted exploit would require some degree of effort and ransomware hackers currently appear most interested in the low hanging fruit represented by poorly patched personal computers. But with around 5,000 hospitals in the US, let's say a ransomeware hacker successfully infects one medical device system in 20% of hospitals (1,000 hospitals). With a ransom of $20,000, that comes to a $20 million payoff — just in the US.
To summarize, a ransomeware exploit specifically targeting medical device systems would require special effort to create. Such an exploit could have a very attractive return on investment. The substantial risk presented by this scenario is fortunately mitigated by the past behavior of ransomeware hackers to target much larger populations of general purpose personal computers rather than taking a targeted approach. Sadly, past behavior is no guarantee of future behavior.
The concept of a clearly-defined corporate perimeter will continue to ‘erode’ in medical institutions, as ever more workstations, servers, mobile devices and equipment go online. This will give criminals more opportunities to gain access to medical information and networks. Keeping defenses and endpoints secure will be a growing challenge for healthcare security teams as every new device will open up a new entry point into the corporate infrastructure.
This does not appear to be a risky prediction, and is reinforced by the continued adoption of remote service capabilities adopted by medical device manufacturers to improve service and support. Telemedicine is another potential avenue of attack for medical devices.
Sensitive and confidential data transmitted between connected ‘wearables’, including implants, and healthcare professionals will be a growing target for attack as the use of such devices in medical diagnosis, treatment and preventative care continues to increase. Pacemakers and insulin pumps are prime examples.
Sorry, but do patients really care who might know their blood glucose levels, how often they exercise, or their progress in quitting smoking? Is this data of any monetary interest to third parties that would be willing to buy the data from criminals? Many of the risks here go back to device availability and basic mobile device privacy issues like who you talk to and where you go, rather than any health related content.
While most data in implantable devices is virtually worthless, the continued use of the device is critical. The challenge here for hackers are those associated with any embedded system device, as described above. The St Jude/Muddy Waters "situation" showed that implantable devices and associated systems like Merlin, can be vulnerable. Developing a ransomware exploit for implanted devices is extremely challenging. Even attacking devices associated with the implanted device, such as the Merlin@Home bedside device are challenging.
While the author mentions data theft, the bigger risk with wearables and implanted devices is the risk of patient injury or death as a consequence of losing availability to the device.
The growing use by consumers of connected health and fitness gadgets will offer attackers access to a vast volume of personal data that is generally minimally protected. The popularity of health-conscious, connected lifestyles means that fitness bracelets, trackers, smart watches, etc. will carry and transmit ever larger quantities of personal data with only basic security – and cybercriminals won’t hesitate to exploit this.
Much like the preceding prediction, I don't see this prediction having much validity in health care. While I don't doubt cybercriminals wouldn't hesitate to exploit this data if they could easily get it, I just don't see any value in the data being exploited.
Disruptive attacks – whether in the form of denial of service attacks or through ‘ransomware’ that simply destroys data (such as WannaCry) – are a growing threat to increasingly digital health care facilities. The ever increasing number of work stations, electronic records management and digital business processes that underpin any modern organization broadens the attack surface for cybercriminals. In healthcare, they take on an extra urgency, as any disruption can in real terms become a matter of life or death.
This prediction is a reformulation of some of the previous predictions. The reference to, "any disruption can in real terms become a matter of life or death," bears comment. Waving the "life or death" flag with regards to data security in health care has not been proven out in the real world – yet. Nor is it very likely that hacked clinical information systems will result in patient injury or death.
When we think of medical devices, we often think of embedded systems like patient monitors, ventilators or infusion pumps. There is a category of medical devices that are just application software running on general purpose personal computers, on a desk top or in a server farm. Like other medical devices, these systems carry real safety-critical risk of patient injury or death. Unlike embedded system medical devices, they may be much more vulnerable to the attentions of a hacker.
Last, but not least, emerging technologies such as connected artificial limbs, implants for smart physiological enhancements, embedded augmented reality etc. designed both to address disabilities and create better, stronger, fitter human beings – will offer innovative attackers new opportunities for malicious action and harm unless they have security integrated from the very first moment of design.
I can't wait to be transformed into a cyborg with intelligent artificial limbs, an exoskeleton and brain implants. Hopefully by the time these devices become actual products (with an installed base sufficiently attractive to hackers) we will have figured out this problem with data security of the Internet of things. This last prediction falls squarely in the domain of medical device manufacturers, rather than the buyers who deploy and use them.
This post is intended to provide a more realistic assessment of the actual risks. The Kapersky prognostications are relatively spot on, with only some dramatic overstatement. The challenge with health care is that "realistic risks" tend to be ignored by manufacturers and their customers alike, and thus persist. Another challenge is the long life cycle of medical devices, sometimes more than ten years. Some hope that a more extreme casting of risks will stir the health care industry to take these risks seriously and mitigate them more aggressively.
Real change is occurring on the manufacturer side as a result of the FDA's cybersecurity guidance and their insistence that manufacturers implement meaningful data security controls in their product development process and products. This is great for new products reviewed by FDA in the past year or so and going forward. This does not address the huge installed base of devices with little or no cybersecurity capabilities purchased before the FDA change.
The lion's share of responsibility for medical device data security falls on the already over burdened shoulders of health care providers. In response to this burden, a growing number of startups are coming to market with solutions specifically for medical devices (and other types of embedded system devices).
The industry will continue to make plodding progress in medical device cybersecurity. However, should a hacker develop an effective exploit for medical devices that is successful in the wild, the status quo will quickly fly out the window.





Trackbacks/Pingbacks