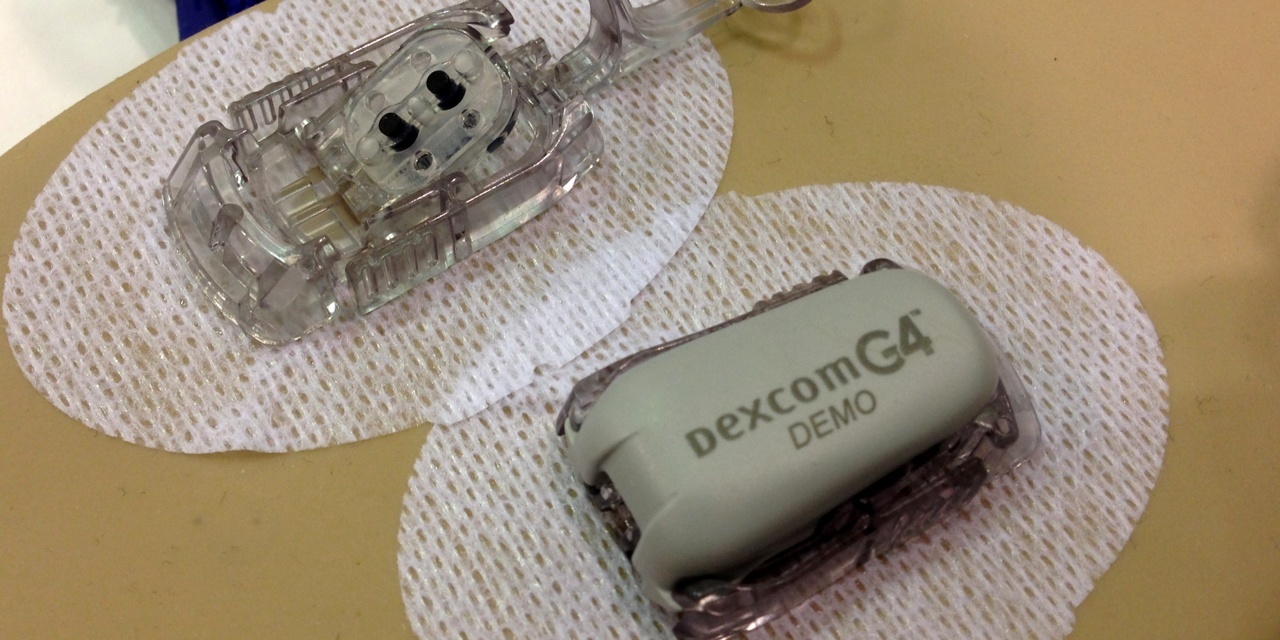
The fact that connectivity, and perhaps wireless connectivity in particular, allows for hacking for mischief, theft, politics, social protest and other forms and varying degrees of evil should surely come as no surprise. In turn, that a wireless medical device might be hackable should be somewhere on the mind of developers, users, and regulators. Thus the report from the recent Black Hat conference that someone hacked an insulin infusion pump (not pictured above), and in so doing was then able to alter its settings, should also not be particularly shocking, but should serve as yet another reminder, that security associated with connectivity has been and continues to be an issue, as was addressed by Tim back in 2006.
The report in this instance came from Jay Radcliffe who hacked his own insulin delivery equipment. In this instance the hacking avenue was the wireless remote that was part of the device. Perhaps the idea that a wireless remote could be emulated is even at the ultra low end of surprise. More generally, the multiple discussions of this report (e.g. here and here) have suggested that the technology being used by at least some medical device manufacturers does not offer an adequate array of security safeguards. Or the manufacturers haven't fully utilized what is available in terms of alternate hardware, or they havn't fully utilized the security features that were available even in the hardware that they were using.
Not surprisingly medical device manufacturers have downplayed the risks of hacking. The manufacturer of the pump in question, Medtronic, responded through a diabetes oriented web site, but apparently not through an actual press release of its own. The responses included that Medtronic does take device security seriously (would you expect them to say otherwise?), and that no real-life events have ever reported. Of course a problem with the later is that stealth hacking, as opposed to announced hacking, could cause harm while going unreported. This is to not say they have, but only to note that "reported" is a limiting case.
Medtronic is quoted further as saying "Our job is to incorporate information security measures into our designs, vigilantly monitor potential threats and to always be proactively finding ways to make our devices more secure for you. That is what we have done and what we will continue to do."
A curious post in response to this expected response from Medtronic was "Security violations are caused by sloppy implementation. The systems themselves are very secure." I'm not sure how much better that is supposed to make us feel. Equally curious was that this response referenced RSA as a security authority, with other posters then pointing out that RSA was itself hacked.
Hypothetically (that means I made up the following) assorted glitches and could-not-duplicate service events could be the result of hacking, i.e. if the hacker hacked, and then stopped hacking, whatever the effect of the hacking was could well stop also, and therefore be un-findable. Which reminds me of a hospital wireless interference anecdote I heard about bursts of interference, almost always during the night, and almost always for one or two minutes. The culprit was an old leaky microwave being used in quick mode. And why only at night? Because the cafeteria was closed then and therefore the microwave was a primary food resource.
The bottom line is that security is an ongoing issue that must be rigorously addressed by manufacturers, and in turn by the FDA who has to at least ask the what-have-you-done-about-connectivity-security, and insist on a firm answer. Further, I will ask the question that I asked about the challenges of hospital networking at an AAMI session last June in San Antonio. My question was, "Is the problem getting easier or harder?" The answer was a laugh.




wow, I’ve seen hacked computers, websites but “insulin pumps” are something totally new!
Thanks for the pic as well 🙂
While it may seem far fetched that a hacker would set out to hack an insulin pump rather than a computer, the fact that it is at possible is cause for concern. Jay Radcliffe hacked his own device, but what’s to stop someone from hacking into a device that belongs to someone else? It’s a scary thought.
This comes as a surprise since the hack is done in the insular pump. I agree that it will serve as a reminder that even something as strange as hacking an insular pump can happen.
I’m rather intrigued by this hack, and the one presented in 2008 that lead to the paper “Pacemakers and Implantable Cardiac Defibrillators: Software Radio Attacks and Zero-Power Defenses.”
As a writer exploring these issues fictionally, I’m obsessed with understanding the underlying technology as to easily translate it for the average reader.
Surfing the Medtronic site, I find their insulin pumps / glucose monitors are able to interface with their “CareLink” software for report generation, but seem to require a remote control to actually reprogram the device.
I see nothing about it’s “Conexus Wireless Telemetry” tech advertised on products available…so how exactly is data transmitted I wonder?
FDA advisory board urges evaluation of hacking risks
http://www.fiercemedicaldevices.com/story/board-urges-evaluation-device-hacking-risks/2012-04-11?utm_medium=nl&utm_source=internal
Medtronic to parley with hacker.
http://go.bloomberg.com/tech-blog/2012-06-27-insulin-pump-hacker-medical-device-maker-come-to-the-table/
July 8, 2012
Fierce Medical posted an interesting timeline and article on the hackability issue.
“Timeline: The industry gets serious about device hacking”
http://www.fiercemedicaldevices.com/pages/timeline-industry-gets-serious-about-device-hacking?utm_medium=nl&utm_source=internal